Cyberattacks today are not always loud or obvious. One of the most dangerous threats facing organizations is the stealer log incident. These incidents happen when malware silently steals usernames, passwords, browser cookies, tokens, and other sensitive data, then uploads them to attacker-controlled servers. Once exposed, this data is often sold or reused for further attacks.
Because stealer malware works quietly, many organizations do not realize they have been compromised until real damage occurs. Below are 10 key strategies to help you detect and respond to stealer log incidents effectively, even if you are new to cybersecurity.
1. Understand What Stealer Logs Are
Stealer logs are collections of stolen credentials and session data gathered by malware such as RedLine, Vidar, Raccoon, or Lumma. These logs may include:
-
Browser-saved passwords
-
Session cookies
-
Email and VPN credentials
-
Crypto wallet information
Knowing what data is at risk helps teams respond faster and more accurately.
2. Monitor for Unusual Login Behavior
One of the earliest signs of a stealer log incident is abnormal login activity, such as:
-
Logins from unfamiliar countries
-
Access at unusual hours
-
Multiple failed login attempts followed by success
Monitoring authentication logs across cloud apps, VPNs, and email systems is critical.
3. Watch for Credential Reuse
Stolen credentials are often reused quickly across different services. If you see the same username attempting to log in to multiple platforms within a short time, this may indicate credential theft.
Implementing alerts for credential reuse patterns can significantly reduce response time.
4. Detect Suspicious Endpoint Behavior
Stealer malware usually runs on endpoints such as laptops or desktops. Warning signs include:
-
Unknown processes running in the background
-
Unexpected browser crashes
-
Disabled antivirus or security tools
Endpoint Detection and Response (EDR) solutions are highly effective for spotting these behaviors.
5. Monitor Data Exfiltration Patterns
Stealers send stolen data out of the network, often in small, encrypted packets. Look for:
-
Frequent outbound connections to unknown domains
-
Traffic to suspicious IP addresses
-
DNS tunneling or abnormal HTTPS traffic
Even small data transfers can signal a major breach.
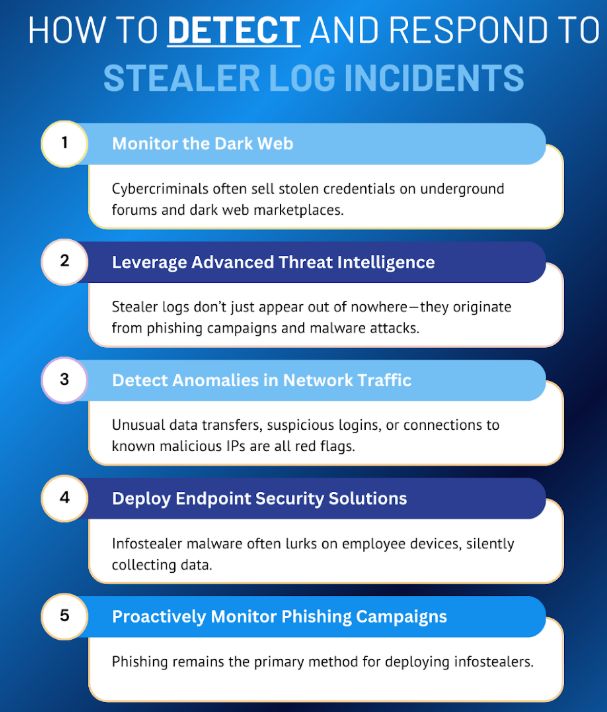
6. Use Threat Intelligence Feeds
Many stealer logs are sold or shared on underground forums and Telegram channels. Threat intelligence feeds can alert you when:
-
Your company domain appears in stealer databases
-
Employee credentials are advertised for sale
-
New stealer malware campaigns emerge
Early awareness allows you to act before attackers do.
7. Reset Credentials Immediately
Once a stealer log incident is suspected or confirmed, speed is critical. Immediately:
-
Reset affected passwords
-
Revoke active sessions and tokens
-
Rotate API keys and access credentials
Delays give attackers more time to move laterally or escalate privileges.
8. Enforce Multi-Factor Authentication (MFA)
MFA significantly reduces the impact of stolen credentials. Even if usernames and passwords are compromised, MFA can prevent attackers from logging in.
Focus first on:
-
Email systems
-
VPN access
-
Cloud admin accounts
-
Financial and HR platforms
9. Isolate and Clean Infected Devices
Any device suspected of being infected must be:
-
Disconnected from the network
-
Scanned or reimaged
-
Fully patched and secured before reuse
In some cases, a full system rebuild is safer than attempting cleanup.
10. Educate Users and Improve Prevention
Most stealer infections start with:
-
Fake software downloads
-
Cracked or pirated applications
-
Malicious email attachments
User awareness training is one of the most effective defenses. Teach employees to:
-
Avoid untrusted downloads
-
Recognize phishing emails
-
Report suspicious behavior early
Prevention is always cheaper than recovery.
Final Thoughts
Stealer log incidents are dangerous because they are quiet, fast, and scalable. A single infected device can expose dozens of accounts and open the door to ransomware, fraud, or espionage.
The good news is that every stealer attack leaves traces. By combining visibility, monitoring, fast response, and user education, organizations can dramatically reduce both the impact and likelihood of these incidents.
Cybersecurity is no longer just about blocking attacks. It is about detecting weak signals early and responding decisively. With the right strategies in place, even small teams can stay one step ahead of stealer-based threats.
As an experienced IT System Integrator, iLogo Malaysia is ready to help your company build a comprehensive cybersecurity strategy—from cybersecurity training and endpoint solutions to the implementation of integrated defense systems.