Tag: iLogo
-

What Is a DDoS Attack? A Simple Guide to Traffic Flooding Threats
In today’s always-online world, websites and digital services are expected to be available 24/7. Whether it’s online banking, e-commerce, or internal business systems, downtime can quickly lead to lost trust and revenue. One of the most common reasons services suddenly go offline is a DDoS attack. While the term sounds technical, the idea behind a…
-

Three Common Mistakes Companies Make When Implementing DMARC
Email remains one of the most trusted and widely used communication tools in business. Unfortunately, it is also one of the easiest ways for attackers to impersonate brands, steal data, and commit fraud. That is why DMARC has become an essential part of modern email security. DMARC (Domain-based Message Authentication, Reporting, and Conformance) helps organizations…
-

10 Key Solutions for More Effective Attack Surface Management
As organizations continue to adopt cloud services, remote work, SaaS applications, and connected devices, their digital footprint keeps growing. Every new system, application, or exposed service increases what is known as the attack surface—all the points where attackers could potentially gain access. Attack Surface Management (ASM) helps organizations discover, monitor, and reduce these entry points…
-

Breaking Down the REvil Ransomware Threat
Ransomware has become one of the most dangerous cyber threats facing organizations today, and REvil (also known as Sodinokibi) is one of the most notorious examples. Responsible for attacks on global companies, REvil shows how modern ransomware has evolved from simple malware into a highly organized criminal operation. This article breaks down what REvil ransomware…
-
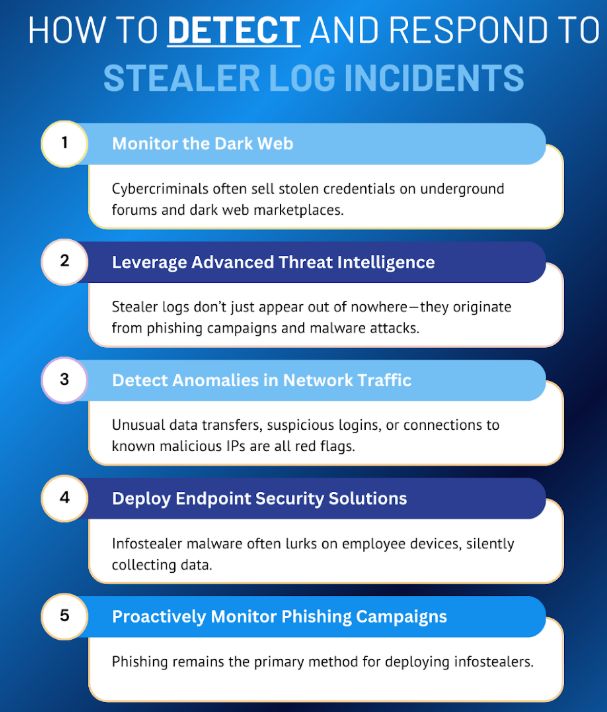
10 Key Strategies to Detect and Respond to Stealer Log Incidents
Cyberattacks today are not always loud or obvious. One of the most dangerous threats facing organizations is the stealer log incident. These incidents happen when malware silently steals usernames, passwords, browser cookies, tokens, and other sensitive data, then uploads them to attacker-controlled servers. Once exposed, this data is often sold or reused for further attacks.…
-

7 Tips for Identifying Suspicious Emails and Avoiding Phishing
Email has become one of the most common ways cybercriminals try to steal sensitive information. Every day, attackers send millions of phishing emails designed to trick people into clicking malicious links, downloading harmful attachments, or revealing personal data. These messages often look surprisingly real, making it difficult for users—especially beginners—to tell the difference between a…
-

Must-Follow Cybersecurity Standards for Every Organization
In today’s digital world, cybersecurity is no longer optional. Every organization—big or small, public or private—depends on technology to operate. This means the risk of cyberattacks continues to grow. Hackers target companies of all sizes, looking for weaknesses they can exploit to steal data, disrupt operations, or demand ransom. To defend against these threats, organizations…
-

Email Security Guide: Implementing DMARC to Protect Your Business Communication
Email remains one of the most important communication tools in the business world. Companies use email to contact customers, suppliers, employees, and partners every day. Because of this, cybercriminals often target email systems to steal data, impersonate organizations, or spread malware. One of the most effective ways to protect your business from email-based threats is…
-

App Hijacking on Android: How Cybercriminals Steal Money — and How You Can Stop It
App hijacking on Android is a growing threat. Instead of making fake apps, attackers sometimes take over real, trusted applications to trick users and steal money. This blog explains how app hijacking works, the tactics criminals use, real-world risks, and clear steps you can take to protect yourself and your organization. What is app hijacking?…
-

October and Cybersecurity Awareness Month: What It Really Means
Every October, people around the world celebrate Cybersecurity Awareness Month. You might have seen it mentioned on social media, in your office newsletter, or even in the news. But what exactly is it? Why does it matter to regular people and businesses? And what can you actually do during this month to stay safer online?…